The Dual-Hub Alpha: How Managed IT Services Empower Asset Managers in Hong Kong and Singapore
Discover how managed IT services enhance operational efficiency and cybersecurity for asset managers in Hong Kong and Singapore. Partner with Brocent for expert IT outsourcing.

The Dual-Hub Alpha: How Managed IT Services Empower Asset Managers in Hong Kong and Singapore In the high-stakes corridors of Hong Kong’s Central district and Singapore’s Marina Bay , the difference between a good year and a great year for an asset manager often comes down to milliseconds and reliable data. For hedge funds , quantitative trading firms , and multi-family offices , technology is no longer a back-office utility—it is the primary engine of "Operational Alpha."
However, the operational reality is brutal. Asset managers in these twin financial capitals face a unique "trilemma":
- Strict Regulatory Scrutiny: Navigating the divergent requirements of the SFC (Hong Kong) and MAS (Singapore).
- Cybersecurity Threats: Protecting high-value proprietary algorithms and client data from sophisticated state-sponsored attacks.
- Cost Efficiency: avoiding the bloat of a massive internal IT department while maintaining "bank-grade" support.
This guide explores how leading firms are partnering with specialized IT Managed Service Providers (MSPs) to design, build, and maintain high-performance environments. We will specifically look at the "Token Service" (Bulk Hours) model—a financial innovation in IT support that is changing how funds manage their burn rate.
1. Design & Build: The "Gold Standard" Infrastructure Foundation
For a new fund or a family office spinning out of a private bank, the "Day 1" setup determines your audit readiness. The "DIY" approach of buying laptops at a retail store is a red flag for institutional investors.
The Tiered Infrastructure Approach
Top-tier MSPs, such as Brocent, utilize a structured framework (often called the "Infrastructure Foundation") to ensure scalability:
- Tier 1: Physical & Cloud Foundation: This involves setting up the "plumbing"—server racks in co-location centers, secure private clouds, and resilient ISP failovers. In Hong Kong, this often means ensuring redundancy between providers like PCCW and HGC to prevent trading halts during fiber cuts.
- Tier 2: Zero-Touch Endpoint Deployment: Modern MSPs use Windows Autopilot to provision devices. A trader receives a sealed laptop, connects to Wi-Fi, and the machine automatically configures itself with all necessary trading software, security patches, and drive mapping. No IT engineer needs to physically touch the device, reducing supply chain risk.
Regulatory Compliance: SFC vs. MAS
A specialized MSP acts as your compliance architect, ensuring your build-out satisfies local regulators:
- Hong Kong (SFC): The focus is on data sovereignty and the "Responsible Officer" (RO) accountability. MSPs ensure that critical client data resides on servers (or Azure regions) physically located within Hong Kong to satisfy PDPO (Personal Data Privacy Ordinance) requirements.
- Singapore (MAS): The Technology Risk Management (TRM) Guidelines are the bible here. MSPs implement rigorous "Privileged Access Management" (PAM) to ensure that no single administrator has unchecked power—a key requirement for MAS audits.
2. Microsoft Intune: The "Invisible" Security Perimeter
In the era of remote work and frequent travel between HK and SG, the "office firewall" is dead. Identity is the new perimeter. Microsoft Intune is the tool MSPs use to enforce security without hindering trader speed.
Policies for the "Roaming" Trader
- Conditional Access: If a portfolio manager attempts to log in from an "untrusted" location (e.g., a public Wi-Fi cafe in a high-risk country), Intune can block the access or demand a hardware-key MFA challenge.
- Automated Compliance Enforcement: Devices are checked for health before they touch the network. If a laptop’s antivirus is outdated or BitLocker encryption is disabled, Intune quarantines the device immediately.
- Mobile Application Management (MAM): For family office principals using personal phones, MSPs can "containerize" corporate apps. This means they can wipe the Outlook app data remotely if the phone is lost, without touching the user's personal photos or contacts.
3. Microsoft 365: From "Email" to "Secure Vault"
A generic Microsoft 365 setup is insufficient for finance. Managed services transform M365 into a secure, compliant data repository.
- Data Loss Prevention (DLP): MSPs configure stringent DLP rules that detect and block sensitive data transmission. For example, if a user tries to email a file containing a pattern matching "Investor Social Security Numbers" or "Proprietary Algo Source Code" to a generic Gmail address, the system blocks it and alerts the Compliance Officer.
- Immutable Archiving (Journaling): To meet the SFC’s record-keeping rules (often 7 years), MSPs set up immutable journaling. Even if a trader deletes an email from their inbox, a tamper-proof copy is retained in a separate archive, ensuring the firm is always audit-ready.
- Secure Collaboration: Configuring Teams and SharePoint with "Least Privilege" access ensures that the "Chinese Wall" between research and trading desks is digitally enforced.
4. Building the Trading Ecosystem: Speed and Stability
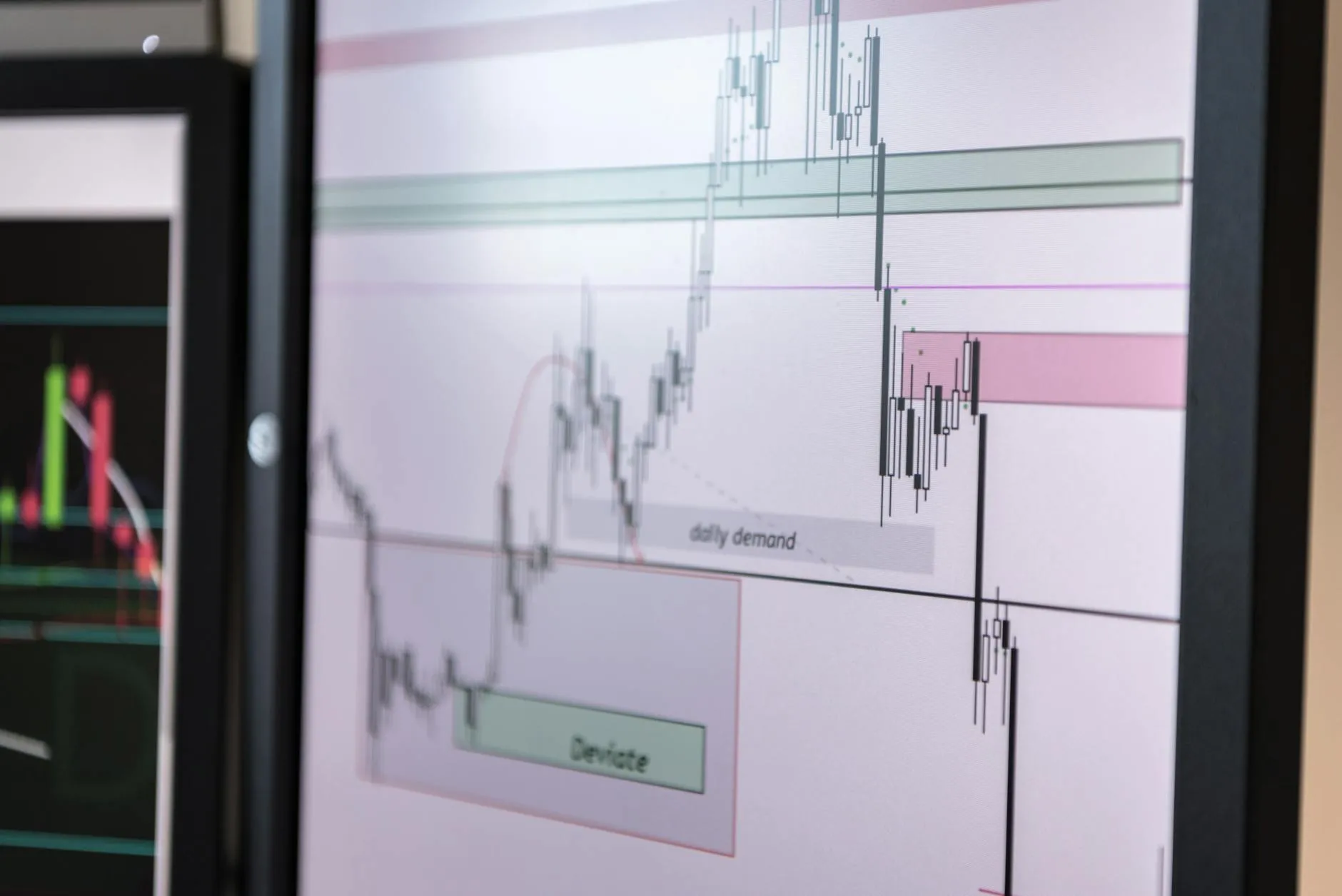
For quantitative firms, the IT environment is the product. Latency is lost revenue.
Low-Latency Connectivity
MSPs design networks that prioritize trading traffic above all else. This involves:
- Direct Market Access (DMA) Paths: Optimizing routing to HKEX (Hong Kong) and SGX (Singapore) data centers.
- SD-WAN Optimization: Using software-defined networking to bond multiple internet lines. If the primary line jitters, traffic seamlessly shifts to the backup without dropping the FIX session.
Vendor Coordination "One-Stop-Shop"
A major pain point for funds is the "blame game" between the ISP, the market data provider (e.g., Bloomberg, Refinitiv), and the OMS vendor. An MSP takes on the role of Vendor Manager , acting as the single technical point of contact to resolve connectivity issues, so traders can focus on the market, not the router.
5. The New Frontier: Data Analysis & LLM Integration
The asset management industry is racing to integrate Large Language Models (LLMs) for research and sentiment analysis. However, the risk of data leakage is massive.
Private AI Infrastructure
Managed service providers are now deploying Private LLM Instances (e.g., via Azure OpenAI Service) that sit inside the client's secure tenant.
- Data Privacy: Unlike the public ChatGPT, these private instances do not train on your data. Your proprietary research stays yours.
- RAG (Retrieval-Augmented Generation): MSPs build "Chat with your Data" systems. An analyst can upload 500 PDF annual reports and ask the private LLM, "Summarize the debt maturity profile differences between Company A and Company B," receiving an answer in seconds with citations.
- Code Copilots for Quants: Securely deploying AI coding assistants that help quants write Python/R scripts faster, while ensuring the code repository remains within the firm's secure perimeter.
6. The "Token Service" (Bulk Hours): A Financial Model for IT Support
Perhaps the most significant value add for a lean asset manager is the shift from "Headcount" to "Tokens." Traditional IT requires either an expensive full-time hire (HK$60k+/month) or a rigid monthly managed service contract.
The Token Service or Block of Hours model offers a third way.
How It Works
The firm pre-purchases a block of engineering hours (e.g., 100 Tokens) that are valid for 12 months.
- 1 Token = 1 Hour of Engineering Time.
- The hours can be used for anything : fixing a broken printer, configuring a new firewall, or high-level consulting.
Why It Saves Cost for Asset Managers
- No "Wasted" Retainer: In a fixed-fee model, you pay HK$20k/month even if nothing breaks. With tokens, you only pay for what you use. If your system is stable, your tokens last longer.
- Access to Tier 3 Experts: A small fund cannot afford a full-time CIO. Tokens allow you to "rent" a Chief Information Officer for 2 hours to review your disaster recovery plan, then switch back to a junior engineer for password resets. You get access to high-level talent without the high-level salary.
- Regional Flexibility: A unique feature of providers like Brocent is cross-border token usage. A token purchased in Hong Kong can often be used for support in Singapore or Tokyo. This is perfect for multi-office family offices that don't want to sign three separate vendor contracts.
7. Business Continuity & Disaster Recovery (BCDR)
In high-density Asian cities, risks aren't just typhoons—they are infrastructure failures.
- Cloud Failover: MSPs implement "Hot Sites" in the cloud. If the office building in Central is inaccessible, the entire desktop environment can be spun up in Azure Virtual Desktop (AVD) within minutes, allowing traders to work from home.
- WORM Backups: To defend against ransomware, backups are stored in Write-Once-Read-Many (WORM) format. Hackers cannot encrypt or delete these backups, ensuring you can always restore your data.
8. Strategic Summary: From Cost Center to Competitive Edge
For the modern asset manager, IT is a strategic partner. By outsourcing the "heavy lifting" of infrastructure design, security monitoring, and helpdesk support, you achieve three critical goals:
- Institutional Credibility: You pass ODD (Operational Due Diligence) with flying colors.
- Scalability: You can add 5 traders or a new office in Singapore without breaking your systems.
- Cost Control: You convert fixed IT headcount costs into flexible, usage-based operating expenses.
In a market where edge is everything, your technology foundation is the one variable you can control completely. Don't let it be the variable that fails you.
Ready to Audit Your Infrastructure? If you want to benchmark your current IT setup against industry standards, I can help you with:
- A Sample "Token Service" Calculator to see how much you could save vs. a full-time hire.
- An SFC/MAS Technology Compliance Checklist to identify immediate gaps.
- A Demo of Private LLM Integration for financial research.
Let me know which of these would be most valuable for your team right now.
Share:
Ready to take action?
Turn these insights into a roadmap for your business.
Book a 15-minute no-obligation consultation with our APAC IT experts. We'll review your current setup and provide a tailored IT roadmap within 24 hours.
Free Checklist
10 Critical Checks Before Expanding IT to Greater China
PIPL compliance, network segmentation, bilingual helpdesk setup, and more — everything your IT team needs before Day 1 in China.
Request the checklist →📬 Monthly Asia IT Insights
China compliance updates, cybersecurity alerts, and IT tips for APAC teams — once a month.
No spam. Unsubscribe anytime.
Related Articles

Apr 29, 2026
Horizon Consulting B.V. IT Infrastructure Modernization Success Story: How BROCENT Helped a Global Management Consulting Leader Complete Microsoft 365 Full-Stack Migration in Just 3 Weeks

Apr 28, 2026
Securing the Global Frontier: An Endpoint MDR Consultant’s Guide to High-Efficiency Intune Strategies
Apr 16, 2026
Quantitative Trading System: Historical Data Collection, Regression Processing Techniques, IT Infrastructure Requirements, and Mainstream Backtesting Frameworks